Can I transfer grades from previous semester? | |
| As a rule, NO. See the general info page. |
How can I add myself to the course mailing list? | |
|
You can do so by clicking the "Auto Update" link on the left bar. Enter your unified Technion username and GR password. The "username" is your username on t2 and campus (or tx),
and the password is the one you had set for it. If you do not have a unified Technion username, please contact the Technion helpdesk, or the unit through which you registered. This is the only way for
accessing you grades, and for submitting electronic exercises. Any Technion student,
including a student in external studies and an external student from other universities, is eligible for a Technion username.
See Help for instructions. 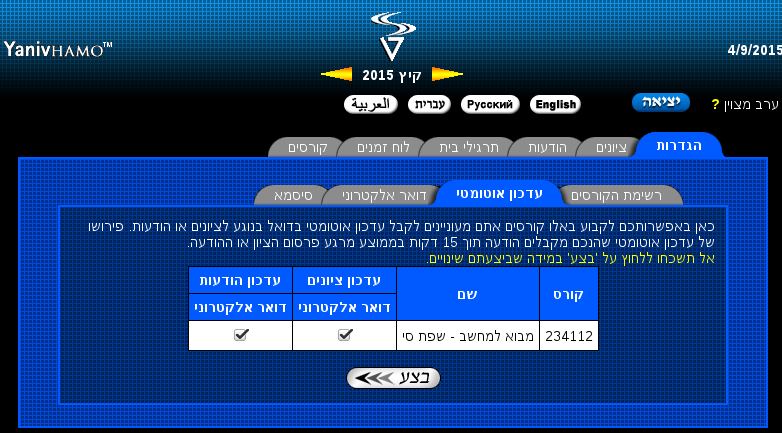
| |
| קישור: Link: Ссылка: وصلة: | https://grades.cs.technion.ac.il/Images/Help/auto-update.png |
In Q3 section 2, there is a reference of "secure software principals". However, they do not appear in the lectures. What should I do? | |
|
Please see the updated slide listing those principles at: https://webcourse.cs.technion.ac.il/236350/Winter2017-2018/ho.html |
In Q3 section 4, the term "Attack surface" is mentioned. What does it mean? | |
|
Please read this short Wikipedia page that describes the term: https://en.wikipedia.org/wiki/Attack_surface |
How can I get the feedback on my assignment? | |
1) Login to your GR++ account (Grades button - using your t2/tx/campus credentials)
2) Head to the homeworks tab.
3) At the relevant assignment, press the backward arrow with the black background.
4) You should get a zip file containing our feedback.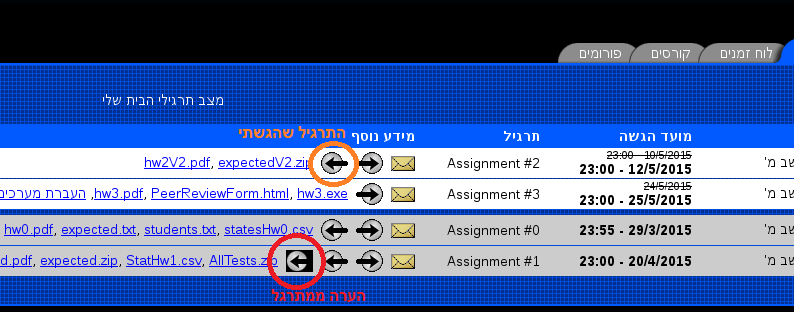 | |
| קישור: Link: Ссылка: وصلة: | https://grades.cs.technion.ac.il/Images/Help/tab-homeworks-ret.png |
Q1: | |
|
We updated the assignment to reflect change in the naming scheme to (VulWebServ-xx instead of VulWebServ-cs2363xx). If you already named your experiment differently, it is OK and just be consistent through out the whole configurations. |
Q1: | |
| Just email Jalil stating which email address we should use for your account. |
Q1: | |
|
Use the following link: http://docs.deterlab.net/core/DETERSSH/#ssh-port-forwarding# |
Q1: | |
|
Fill the forgot password with the following details: username: cs2363xx phone: 1111111111 (if you have not changed it). |
Q1: | |
| Most probably that you created the tunnel inside the users.create.iucc.ac.il server rather in your own computer. Be sure that you create the tunnel from a local terminal.7 |
Q1: | |
|
We found out that one vulnerability that some of used, corrupted part of the server's SQL DB. Thus, you will not be able to provide the "print screen". If you encounter such case, please provide a "print screen" of the shopping cart before the attack rather than the "My Account". |
Q2: | |
| The mail servers and the clients contact each other using SMTP protocol. When filling the tables, you should enable / prohibit it accordingly to the policy. |
Q3: | |
| The blocks contains the grades padded with 0's in front of them. |